Managing Integrations
The Integrations page connects RubixKube with your existing tools for notifications, metrics, workflows, and agent capabilities.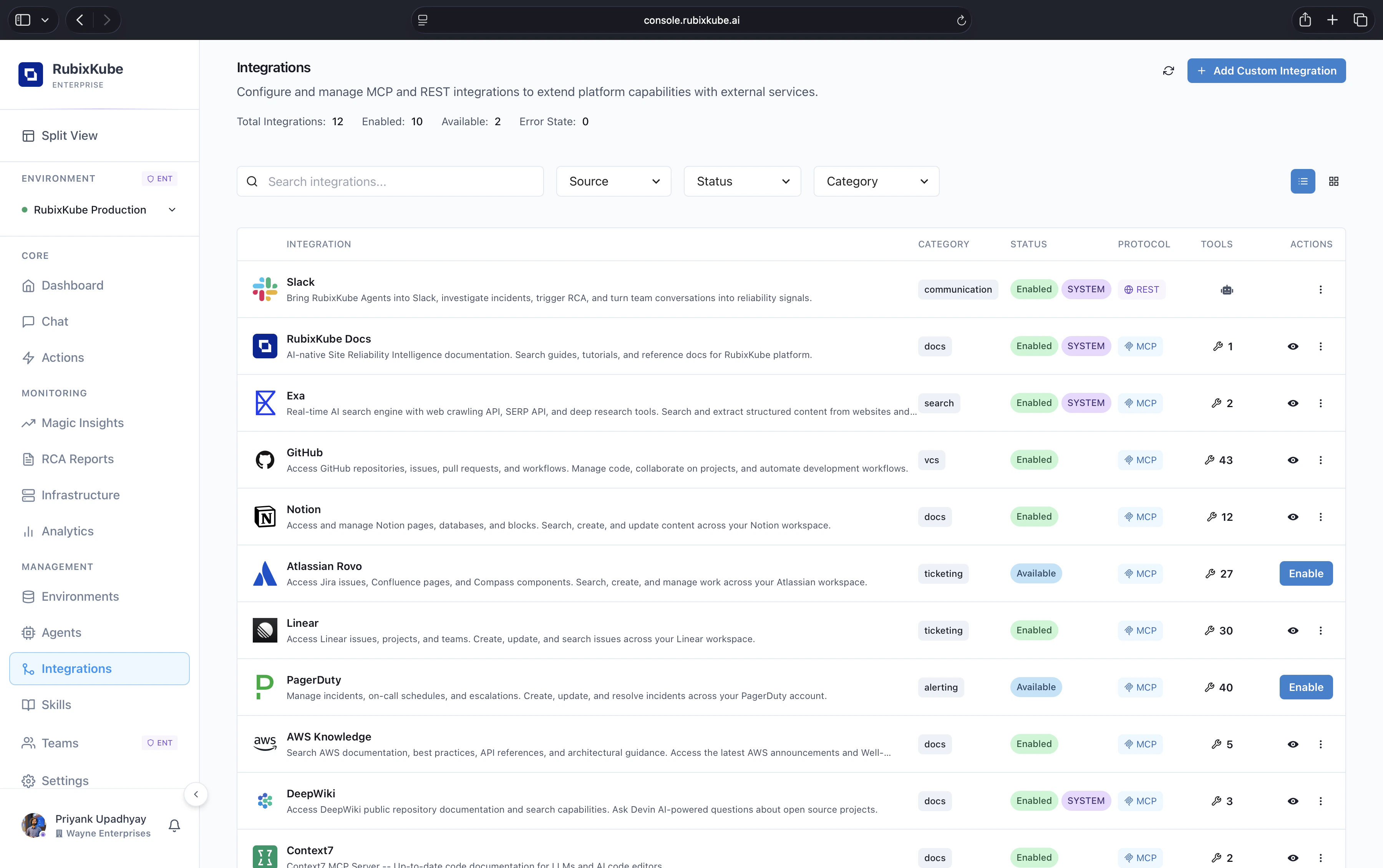

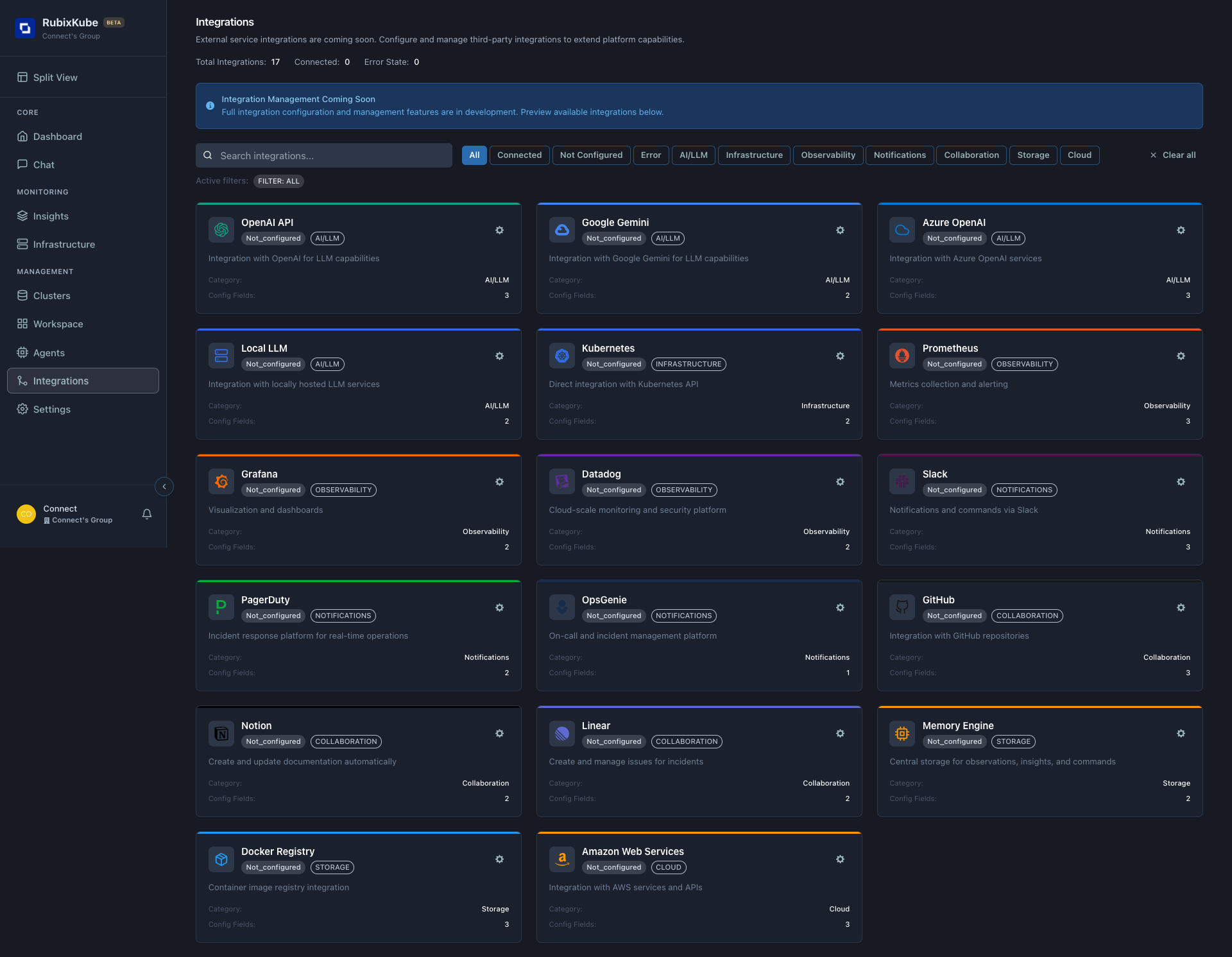
System Integrations
Slack
Get incident notifications in Slack
Setup:- Click “Connect Slack”
- Authorize RubixKube app
- Select channel for alerts
- Configure notification rules
PagerDuty
Page on-call for critical incidents
Setup:- Click “Connect PagerDuty”
- Enter integration key
- Map severity levels
- Test integration
Prometheus
Enhanced metrics collection
Setup:- Enter Prometheus endpoint
- Configure scrape interval
- Verify connection
Webhooks
Notification Rules
Configure when to be notified: - HIGH severity incidents only- All incidents
- RCA report completion
- Cluster disconnection
- PagerDuty alerts
- Webhook calls
- Email (coming soon)
Custom Integrations
Custom Integrations let you connect your own private MCP servers and REST APIs to RubixKube. Once registered, their tools appear automatically alongside system integrations — available to the SRI Agent through Chat, with zero extra plumbing.Enterprise feature. Custom integrations are available on the Enterprise plan. Free and Pro tenants will see a
403 response.Two Protocols
Custom integrations support two protocols. Choose based on what you’re connecting:MCP Server
Connect a private Model Context Protocol server — the same standard used by system integrations. Supports SSE, HTTP, and stdio transports.Best for: MCP-native tools like Linear, GitHub, Notion, or any server that speaks MCP.
REST API
Expose any REST API as agent tools by defining tool schemas and HTTP mappings. No MCP server needed — RubixKube translates tool calls to HTTP requests.Best for: Internal APIs, ticketing systems, CMDB, or any service with a REST endpoint.
Adding an MCP Server
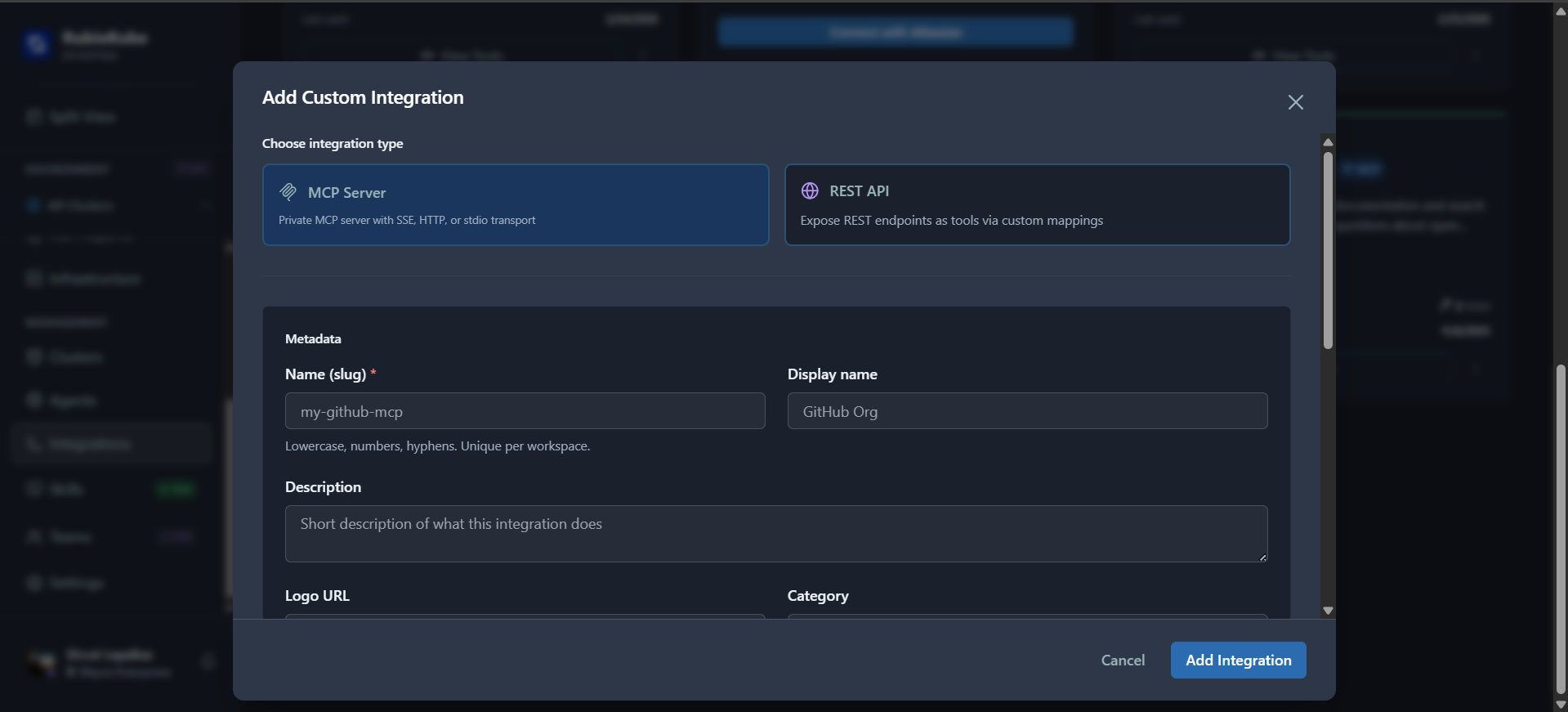
Fill in Metadata
| Field | Description |
|---|---|
| Name | URL-safe slug (lowercase, numbers, hyphens). Unique per tenant |
| Display Name | Human-readable name for the integration card |
| Description | Short description of what this integration does |
| Logo URL | URL to the integration’s logo/icon |
| Category | Category for filtering (e.g., version_control, project_management) |
Configure MCP Connection
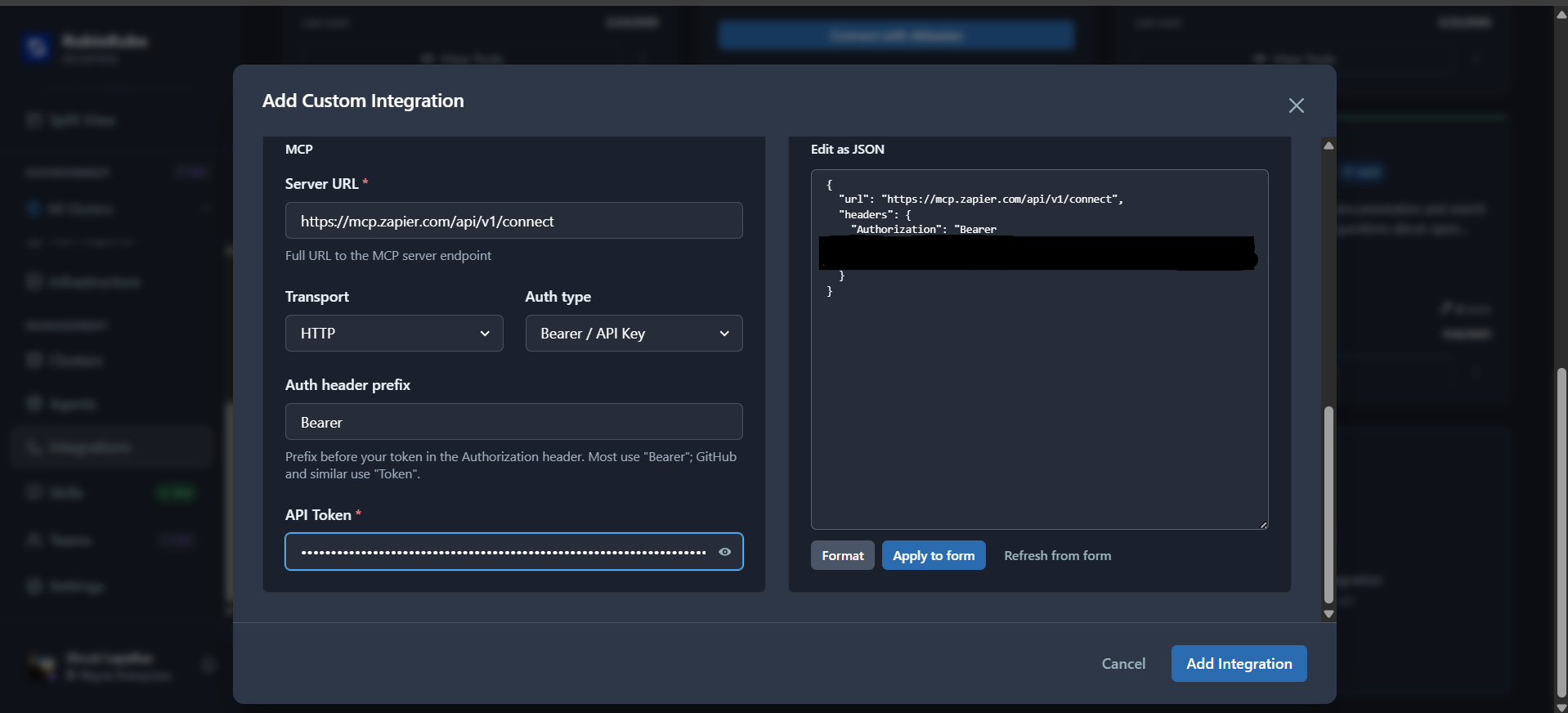
| Field | Description |
|---|---|
| Server URL | Full URL to your MCP server endpoint (e.g., https://mcp.zapier.com/api/v1/connect) |
| Transport | SSE (default), HTTP, or stdio |
| Auth Type | Bearer / API Key (default), OAuth2, or None |
| Auth Header Prefix | Prefix for the Authorization header (default Bearer, use Token for GitHub) |
| API Token | Your authentication token |
Adding a REST API
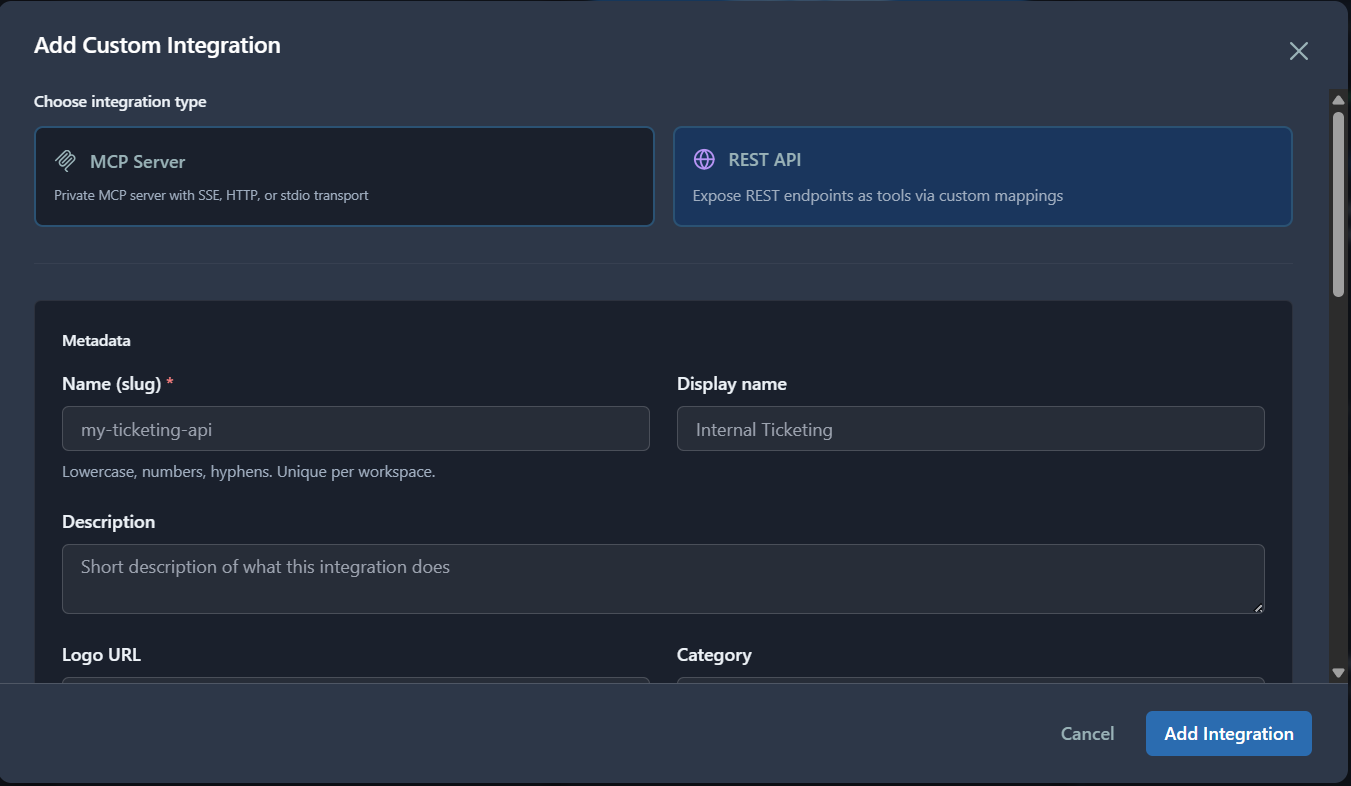
Enter Metadata
Fill in the metadata fields: Name (slug), Display Name, Description, Logo URL, and Category.
Enter Base URL and Auth
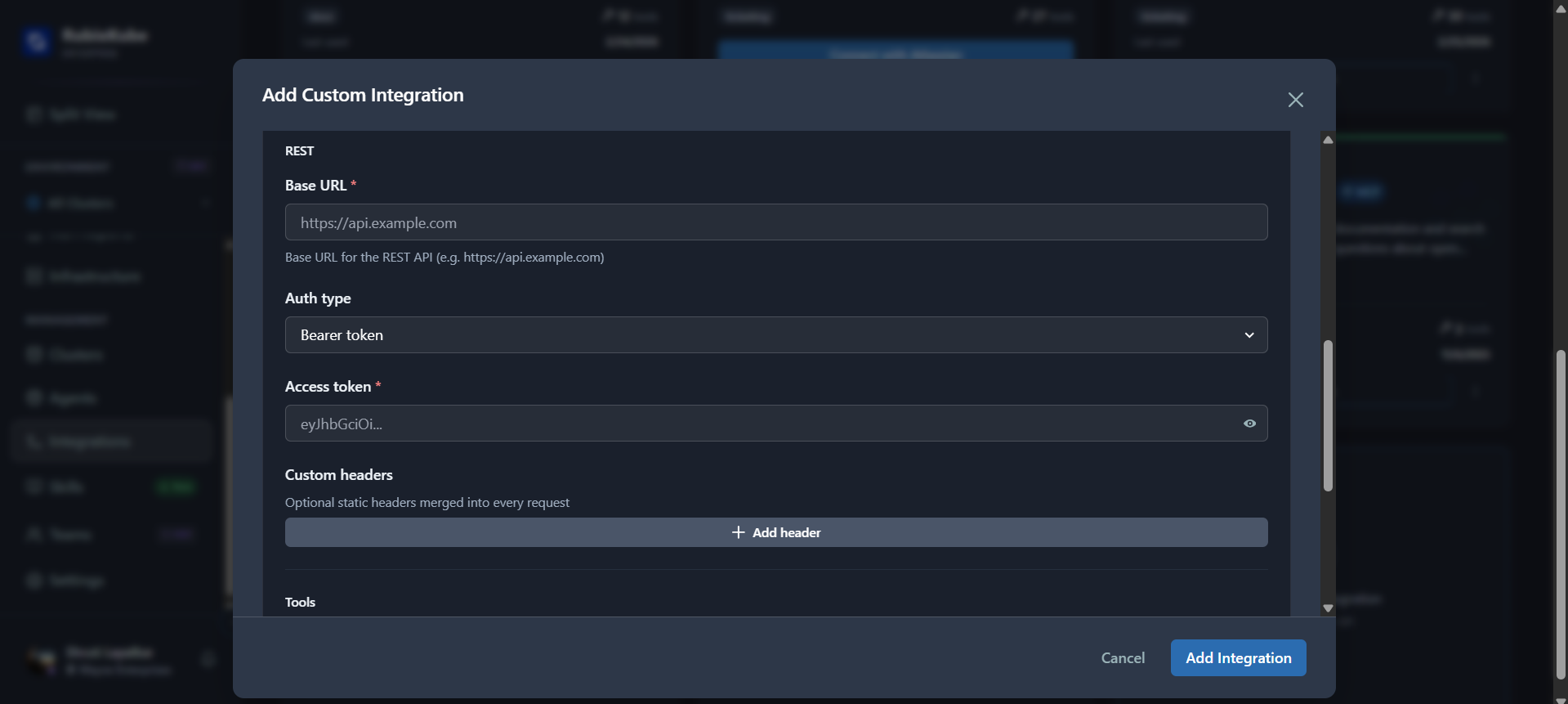
| Field | Description |
|---|---|
| Base URL | Base URL of your API (e.g., https://api.example.com) |
| Auth Type | Bearer token, API Key, Basic auth, or OAuth2 |
| Access Token | Your authentication token (encrypted at rest) |
| Custom Headers | Optional static headers merged into every request (click + Add header) |
Define Tools
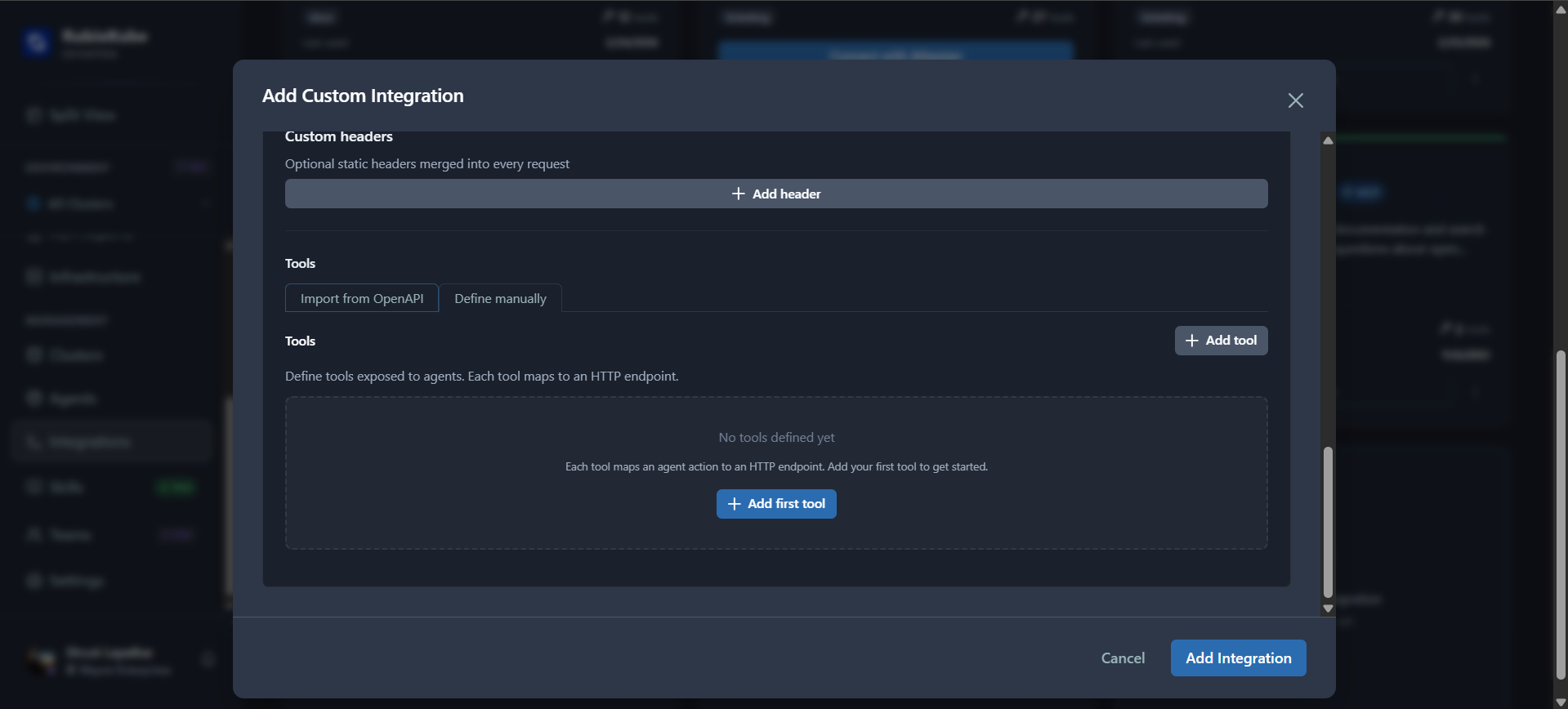
- Import from OpenAPI — upload or paste an OpenAPI 3.x / Swagger 2.0 spec to auto-generate tools
- Define manually — click + Add tool to define each tool by hand
| Field | Description |
|---|---|
| Name | Tool identifier (e.g., list_tickets) |
| Description | What the tool does — the agent reads this to decide when to use it |
| HTTP Method | GET, POST, PUT, PATCH, or DELETE |
| Path | URL path appended to the base URL (supports path params like /tickets/{id}) |
| Parameters | Query params and body params for the tool |
Managing Custom Integrations
Editing a Custom Integration
To update an existing custom integration, click on its card in the catalog and select Edit. The edit form opens pre-populated with all current values.Open the Integration Card
Find the custom integration in the catalog. Custom integrations are shown in the Custom section below the system integrations.
Update Fields
Modify any metadata or connection settings:
| Field | Behavior on Update |
|---|---|
| Display Name / Description / Logo URL / Category | Updated immediately |
| Connection settings (URL, transport, etc.) | Replaced on save |
| Credentials (API token, OAuth config) | Passing new credentials replaces them entirely (re-encrypted). Omit to preserve existing credentials. |
| Tools | Add, remove, or redefine tool schemas |
Other Integration Actions
Disable / Re-enable — Toggle the integration’s status betweenactive and disabled. Disabled integrations are excluded from the MCP gateway.
Tool Filtering — Control which tools are available to agents:
- Enabled tools — allowlist of specific tool names. Empty means all tools allowed.
- Disabled tools — blocklist applied after the allowlist. If a tool appears in both, it’s blocked.
Authentication
Credentials are passed plaintext on create — the server encrypts them before storing. They are always masked in responses.MCP — Bearer Token
MCP — Bearer Token
MCP — OAuth 2.1 (Authorization Code)
MCP — OAuth 2.1 (Authorization Code)
MCP — OAuth 2.1 (Client Credentials)
MCP — OAuth 2.1 (Client Credentials)
For server-to-server flows:
MCP — No Auth
MCP — No Auth
Set
auth_type: “none” and omit credentials entirely.REST — Bearer Token
REST — Bearer Token
api_token or token.REST — API Key
REST — API Key
REST — Basic Auth
REST — Basic Auth
OAuth Flows
For OAuth-based integrations, RubixKube handles the full authorization code flow:Create the Integration
Register the integration with
auth_type: “oauth2” and your OAuth credentials (client ID, secret, URLs).Authorize
Click Authorize on the integration card. This opens the OAuth provider’s consent page in a popup or redirect.
Complete Consent
After you approve, the provider redirects back to RubixKube’s callback endpoint. Tokens are automatically encrypted and stored.
OAuth discovery: RubixKube can auto-discover authorization and token URLs from the MCP server’s
.well-known/oauth-authorization-server or the standard OIDC .well-known/openid-configuration endpoint.How Custom Integrations Appear to Agents
Once created, custom integration tools surface automatically in the tenant’s MCP gateway alongside system integration tools:- Tool discovery — custom tools appear in
tools/listanddiscover_tools() - Tool execution —
tools/callroutes to your server or API with the configured auth - Namespacing — tools are namespaced by the integration’s
nameslug
There’s no difference between a system integration tool and a custom integration tool from the agent’s perspective. Both go through the same MCP gateway.
Custom vs System Integrations
| System Integrations | Custom Integrations | |
|---|---|---|
| Source | Global registry (managed by RubixKube) | Tenant self-served |
| Protocol | Determined by registry | mcp or rest (your choice) |
| Visibility | All tenants (based on config) | Your tenant only |
| Tool definitions | From registry | You provide them |
| Deletion | Disable only | Hard delete |
| Plan | All plans | Enterprise only |
What You Learned
- Available system integrations (Slack, PagerDuty, Prometheus, Webhooks)
- Notification rules and delivery channels
- How to register private MCP servers and REST APIs as custom integrations
- Authentication options: Bearer, OAuth 2.1, API Key, Basic Auth
- How custom integrations appear automatically in the MCP gateway
Related Guides
- Using Agent Skills — Extend agents with structured workflows
- Using Agents & Tools — Monitor agent health and capabilities
- Dashboard — Your command center for infrastructure health
Need Help?
Contact Support
Email: connect@rubixkube.ai
Please include your Tenant ID (Settings → Organization), timestamp, and screenshots.
Please include your Tenant ID (Settings → Organization), timestamp, and screenshots.
Troubleshooting Guide
Step-by-step fixes for common issues across Dashboard, Insights, Agents, and more.
FAQ
Answers to common questions about setup, RCA, agents, and docs.
Docs Navigation
Browse all guides to learn workflows and best practices.